
Thunderstrike 2 will obliterate your Mac, as in, you’ll have to throw it in a bin, and burn the bin. You see, this worm will remain embedded in your Apple computer even after you format your hard drive, and reinstall your OS.
Researchers will demo their malware at Black Hat, and Def Con. The almost impossible to detect, and tough as a cookie firmware is already starting to get on many Apple users nerves.
When you claim that you built something unhackable, you’re signalling every hacker on the planet that there’s a challenge waiting to be overcome. Macs are were considered to be more stable than PCs which have backdoors, and other security breaches.
Good thing hackers can’t do this remotely, right? Welp, better pack your bags and head to the Moon, because researchers have found a way to remotely infect Macs with Thunderstrike 2.
Dubbed the Mac-Ender, the Thunderstrike 2: Sith Strike creators Xeno Kovah, Trammell Hudson, and Corey Kallenberg will present their firmware at Black Hat on the 6th of August. If you want to see the power of the dark side in action, you better get to the six day event in Las Vegas. It already started on the 1st of August.
Researcher Xeno Kovah notes that Macs are susceptible to firmware attacks exactly like PCs, and five out of six vulnerabilities found in PCs are also present in Macs.
Thunderstrike 2 runs automatically when you first boot your Mac, and hackers only need just a few seconds to infect your device with the kratocratic firmware.
Apple’s Macs aren’t superior, even though the majority thinks so, and Kovah notes that whenever you hear about EFI firmware attacks, you should know, that all the x86 machines are targeted.
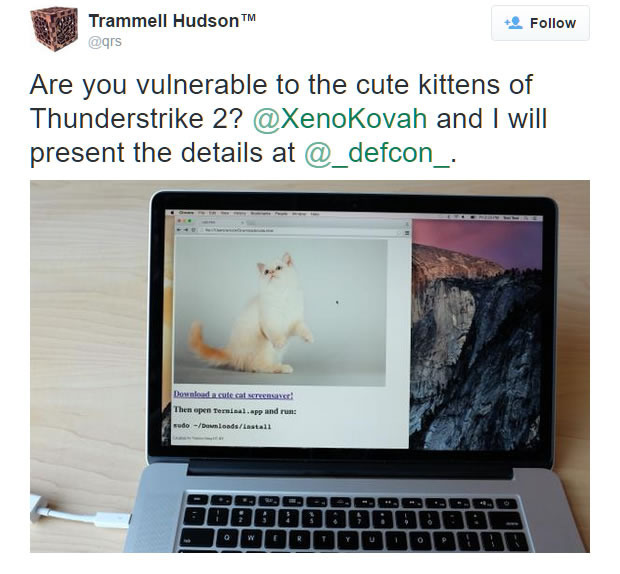
How remotely can hackers get? Your machine can get infected through the traditional phishing method, or through simple malicious websites that implant the firmware. The Sith Strike doesn’t even need machines network-connected to each-other in order to spread like the black plague. It can automatically transmit itself to other peripherals that have the ROM option – like the Apple Thunderbolt Ethernet adapter.
Apple has been notified of the issue, and is fully aware of what this entails for them. As we are accustomed with, there are no official statements from the big A.
After their 6th of August Black Hat presentation, researchers that have worked on the Thunderstrike 2 will release tools for free that will let users check their ROM options on their machines.
The trio will also demo their firmware malware at Def Con on the 8th of August.
