The struggle between security developers and hackers is very likely to never end. However, thanks to a new device called PoisonTap, hackers and actors with ill intents may have gained an upper hand in the ongoing struggle, if they can get the hands on it at least.
Although developers and hackers are at odds with each other, a big part of their jobs involves discovering new ways to hack and access computers. The difference lies in what they do with their knowledge. For example, Samy Kamkar, a very well-known developer as well as a hacker, was created a $5 tool he’s calling Poison Tap. It can be used to access password-protected computers in less than a minute as long as there is a browser running.
According to Kamkar, PoisonTap is built on an extremely cheap Raspberry Pi Zero microcomputer. Anyone can connect it to a computer’s USB port and it will start an automatic process without the need of the actual owner of the PoisonTap to know anything about how it operates.
Nonetheless, Kamkar has provided a detailed description of the process. When the device is connected to a computer, it emulates a network device and starts attacking all outbound connections just by pretending to be the source of the internet. As such, it manages to trick the computer into sending all of its traffic to the device.
Using this method, hackers can easily steal a user’s cookies from their own computer and use the information from them to log-in to the same sites as them. They don’t even need any password or username information to do it. However, the PoisonTap is unable to access information from websites using HTTPS web encryption.
Nonetheless, according to security experts who reviewed Kamkar’s invention claimed it was a new way to attack and bypass a computer’s security. It manages to exploit the excessive amount of trust Windows and Mac computers allow for network devices. They are designed in such a way that when a network device or anything that appears like one is connected, the computer automatically starts exchanging data with it.
As dangerous as the new hack sounds, you have to know that it has limitations. First of all, it’s not a remote hack. Anyone who gets their hands on a PoisonTap have to get access to your physical computer in order to hack it. Caution in not leaving your computer unsupervised is the best measure against such as hack.
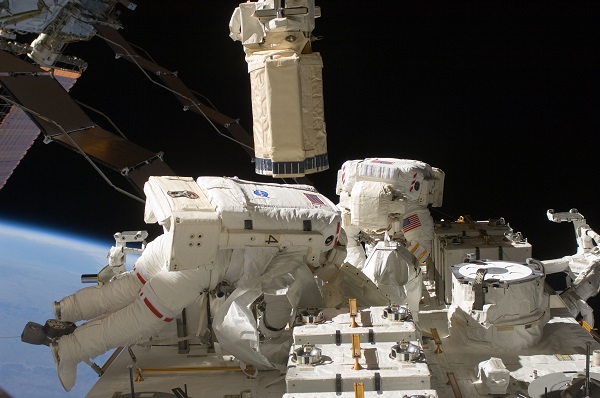
Image source: Wikipedia